Unlock Check Point Certified Security Administrator (CCSA)
Raheem ace
2:35:54
Description
Check Point Security Essentials: Advanced Threat Prevention, Firewalls, and Security Strategies. CCSA R81.20 Preparation
What You'll Learn?
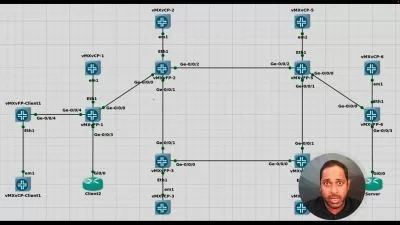
- Understanding the architecture, components, and role of Check Point in cybersecurity.
- Managing security policies, layers, and rules using SmartConsole.
- Best practices for managing network objects, user roles, and administrator privileges.
- Deploying and configuring Check Point Security Gateways, including Network Address Translation (NAT) and firewall technologies.
- Setting up and managing site-to-site and remote access VPNs.
- Using tools like SmartView Tracker, SmartEvent, and SmartView Monitor for real-time monitoring and event analysis.
- Implementing advanced firewall rules, threat prevention, and data loss prevention strategies.
- Ensuring high availability with ClusterXL, and optimizing performance with SecureXL and CoreXL.
- Best practices for backup, disaster recovery, and maintaining system continuity.
- Auditing policies, ensuring compliance with industry standards, and handling security incidents effectively.
- and much more
Who is this for?
What You Need to Know?
More details
DescriptionIMPORTANT before enrolling:
This course is designed to complement your preparation for certification exams, but it is not a substitute for official vendor materials. It is not endorsed by the certification vendor, and you will not receive the official certification study material or a voucher as part of this course.
Welcome to comprehensive Check Point Certified Security Administrator (CCSA) Certification Course.
This course provides a comprehensive understanding of Check Point Software Technologies, equipping learners with the knowledge and skills needed to manage and secure modern networks.
Check Point Certified Security Administrator (CCSA) certification is an entry-level credential that validates a candidate's skills and knowledge in configuring, managing, and troubleshooting Check Point Security Gateway and Management Software Blade systems. The CCSA certification focuses on foundational topics related to network security management using Check Point's security solutions, making it an ideal starting point for network and security administrators.
Starting with an introduction to Check Point, its core components, and its role within the cybersecurity landscape, the course delves into the architecture that underpins Check Point's security solutions. Participants will gain a solid foundation in security management, understanding the roles and responsibilities of various components within Check Point's ecosystem.
The course emphasizes the importance of security policies, offering a detailed exploration of policy creation, management, and execution. Learners will be introduced to Check Point’s SmartConsole, the primary interface for managing security policies and objects. Through hands-on guidance, they will learn to navigate SmartConsole, manage policy layers, rule bases, and objects, and understand the order and execution of policies. Object management is also covered, with best practices for organizing and maintaining network assets.
A key part of the course focuses on user and role management, addressing how to configure and manage different types of users and administrators, while also providing insight into security management servers, backup, and redundancy strategies.
The course shifts to Check Point Security Gateways, exploring their deployment, network address translation (NAT) methods, and the inner workings of Check Point's firewall technologies. Participants will learn the concepts of stateful inspection, security zones, and interfaces, while also gaining exposure to VPN technologies, including site-to-site and remote access VPNs.
Monitoring and reporting play a crucial role in maintaining secure environments, and this course covers Check Point’s tools for log management, event analysis, and real-time monitoring, such as SmartView Tracker, SmartEvent, SmartReporter, and SmartView Monitor. Learners will be guided through generating reports, analyzing security events, and understanding network activity in real-time.
For those interested in advanced topics, the course provides in-depth coverage of advanced firewall concepts, threat prevention technologies like Anti-Bot and Antivirus, as well as the application control and URL filtering capabilities of Check Point. Participants will also learn about the Intrusion Prevention System (IPS) and Data Loss Prevention (DLP) features, offering robust protections against a variety of threats.
Finally, the course addresses high availability and performance optimization using ClusterXL, SecureXL, and CoreXL, ensuring participants understand how to build highly available, redundant, and scalable network security solutions. Backup and recovery strategies are also discussed, equipping learners with the best practices for disaster recovery and system continuity.
Throughout the course, best practices for security management, policy auditing, compliance with industry standards, and incident response will be emphasized, providing learners with a holistic view of Check Point's role in managing and protecting network infrastructures.
By the end of this course, participants will be equipped with the tools and knowledge to effectively manage and secure networks using Check Point technology.
Thank you
Who this course is for:
- Network and Security Administrators – Professionals responsible for managing and securing networks using Check Point technologies.
- IT Professionals – Individuals looking to expand their knowledge in cybersecurity and network security management.
- System Engineers – Engineers involved in designing and implementing secure network infrastructures.
- Cybersecurity Enthusiasts – Anyone with a strong interest in learning about network security, firewall technologies, and advanced threat prevention.
- Check Point Users – Those already using Check Point products who want to deepen their understanding of its features and best practices.
- Aspiring Check Point Certification Candidates – Individuals preparing for Check Point certifications like CCSA (Check Point Certified Security Administrator) or CCSE (Check Point Certified Security Expert).
IMPORTANT before enrolling:
This course is designed to complement your preparation for certification exams, but it is not a substitute for official vendor materials. It is not endorsed by the certification vendor, and you will not receive the official certification study material or a voucher as part of this course.
Welcome to comprehensive Check Point Certified Security Administrator (CCSA) Certification Course.
This course provides a comprehensive understanding of Check Point Software Technologies, equipping learners with the knowledge and skills needed to manage and secure modern networks.
Check Point Certified Security Administrator (CCSA) certification is an entry-level credential that validates a candidate's skills and knowledge in configuring, managing, and troubleshooting Check Point Security Gateway and Management Software Blade systems. The CCSA certification focuses on foundational topics related to network security management using Check Point's security solutions, making it an ideal starting point for network and security administrators.
Starting with an introduction to Check Point, its core components, and its role within the cybersecurity landscape, the course delves into the architecture that underpins Check Point's security solutions. Participants will gain a solid foundation in security management, understanding the roles and responsibilities of various components within Check Point's ecosystem.
The course emphasizes the importance of security policies, offering a detailed exploration of policy creation, management, and execution. Learners will be introduced to Check Point’s SmartConsole, the primary interface for managing security policies and objects. Through hands-on guidance, they will learn to navigate SmartConsole, manage policy layers, rule bases, and objects, and understand the order and execution of policies. Object management is also covered, with best practices for organizing and maintaining network assets.
A key part of the course focuses on user and role management, addressing how to configure and manage different types of users and administrators, while also providing insight into security management servers, backup, and redundancy strategies.
The course shifts to Check Point Security Gateways, exploring their deployment, network address translation (NAT) methods, and the inner workings of Check Point's firewall technologies. Participants will learn the concepts of stateful inspection, security zones, and interfaces, while also gaining exposure to VPN technologies, including site-to-site and remote access VPNs.
Monitoring and reporting play a crucial role in maintaining secure environments, and this course covers Check Point’s tools for log management, event analysis, and real-time monitoring, such as SmartView Tracker, SmartEvent, SmartReporter, and SmartView Monitor. Learners will be guided through generating reports, analyzing security events, and understanding network activity in real-time.
For those interested in advanced topics, the course provides in-depth coverage of advanced firewall concepts, threat prevention technologies like Anti-Bot and Antivirus, as well as the application control and URL filtering capabilities of Check Point. Participants will also learn about the Intrusion Prevention System (IPS) and Data Loss Prevention (DLP) features, offering robust protections against a variety of threats.
Finally, the course addresses high availability and performance optimization using ClusterXL, SecureXL, and CoreXL, ensuring participants understand how to build highly available, redundant, and scalable network security solutions. Backup and recovery strategies are also discussed, equipping learners with the best practices for disaster recovery and system continuity.
Throughout the course, best practices for security management, policy auditing, compliance with industry standards, and incident response will be emphasized, providing learners with a holistic view of Check Point's role in managing and protecting network infrastructures.
By the end of this course, participants will be equipped with the tools and knowledge to effectively manage and secure networks using Check Point technology.
Thank you
Who this course is for:
- Network and Security Administrators – Professionals responsible for managing and securing networks using Check Point technologies.
- IT Professionals – Individuals looking to expand their knowledge in cybersecurity and network security management.
- System Engineers – Engineers involved in designing and implementing secure network infrastructures.
- Cybersecurity Enthusiasts – Anyone with a strong interest in learning about network security, firewall technologies, and advanced threat prevention.
- Check Point Users – Those already using Check Point products who want to deepen their understanding of its features and best practices.
- Aspiring Check Point Certification Candidates – Individuals preparing for Check Point certifications like CCSA (Check Point Certified Security Administrator) or CCSE (Check Point Certified Security Expert).
User Reviews
Rating
Raheem ace
Instructor's Courses
Udemy
View courses Udemy- language english
- Training sessions 27
- duration 2:35:54
- Release Date 2025/01/16