Python For Ethical Hackers and Cyber Security Engineers
Bilel Chatti
4:30:02
Description
Become an Ethical Hacker and Cyber Security Analyst, and build your own hacking tools using Python Scripting
What You'll Learn?
- Python scripting and Ethical hacking
- Write your own hacking tools using python
- Build a strong foundation in networking protocols
- Build a strong foundation in cryptography
- Learn the OSI model, data encapsulation and how network packets are constructed and transferred from one machine to another
- Write you own python script to spoof your MAC address
- Dive Deep into ARP protocol and build a network scanner to discover live hosts
- Acquire a comprehensive understanding of the IP and ICMP protocol
- Lean how to build your own hacking tool to trace route an IP address
- Learn the TCP protocol, how an connection is established during a TCP handshake and the type of TCP packets
- Dive Deep into TCP port Scanning techniques like SYN_SCAN, ACK_SCAN and FIN_SCAN
- Write a python script to scan TCP ports
- Lean data encoding, hashing and encryption
- Build a password cracker in python, to retrieve a password from a given hashing
- build your hacking tool to encrypt and decrypt data using AES algorithm
- Implement an Hybrid Encryption in python, by generating an RSA private and public keys and encrypting the AES session Key
- Learn the fundamentals about Bind Shell and Reverse Shell
- write your own Bind Shell in python language
- write your own reverse Shell in python language
Who is this for?
What You Need to Know?
More details
DescriptionThis course is focused on learning by doing. In this course you will learn both Ethical Hacking and Programming at the same time. First you learn the basic theoretical knowledge about a given topic, then you apply this knowledge by building a hacking tool using python scripting.
On this course we will focus on the following topics, networking, shell terminals and cryptography.
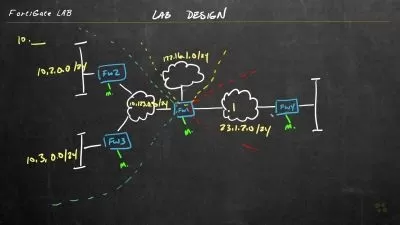
1- We dive into details about the OSI model, data encapsulation and how network packets are constructed and exchanged between different hosts.
2- We learn how data is exchanged using both the MAC address and the IP address.
3- We write a python script that will spoof our MAC address.
4- We learn the inner working of the ARP protocol and we apply that knowledge by writing a network scanner using python scripting. A network scanner will discover all live hosts inside our local network using ARP Requests and Replies.
5- We dive into details about IP protocol and ICMP protocol, and we apply this theoretical knowledge by writing a python script that will trace route an IP address and discover all the routers in the path to the target IP address.
6- We build the required knowledge about TCP protocol, how a connection is made during TCP handshake, and how to scan a target host to discover its open ports using TCP port scanning techniques. We write a python script to scan for open ports using TCP_SYN_SCAN, TCP_ACK_SCAN, TCP_FIN_SCAN...
7- We learn how to connect to a target machine and get a shell terminal to execute commands on this target machine, using BIND SHELL and REVERSE SHELL. We write a BIND SHELL and REVERSE SHELL using python scripting.
8- We learn the fundamentals skills about Cryptography, like Data Encoding, Data Hashing, Data Encryption/Decryption, and Password Hash Cracking.
9- We apply the theoretical knowledge about Cryptography by implementing an Hybrid Encryption in Python using RSA Asymmetric Encryption and AES Symmetric Encryption.
10- We write a Password Hash Cracking Tool using Python Scripting.
Who this course is for:
- Beginners and cyber security enthusiasts who want to follow an Ethical Hacking career
- System administrators and network administrators who aim to improve the defense of their infrastructure
This course is focused on learning by doing. In this course you will learn both Ethical Hacking and Programming at the same time. First you learn the basic theoretical knowledge about a given topic, then you apply this knowledge by building a hacking tool using python scripting.
On this course we will focus on the following topics, networking, shell terminals and cryptography.
1- We dive into details about the OSI model, data encapsulation and how network packets are constructed and exchanged between different hosts.
2- We learn how data is exchanged using both the MAC address and the IP address.
3- We write a python script that will spoof our MAC address.
4- We learn the inner working of the ARP protocol and we apply that knowledge by writing a network scanner using python scripting. A network scanner will discover all live hosts inside our local network using ARP Requests and Replies.
5- We dive into details about IP protocol and ICMP protocol, and we apply this theoretical knowledge by writing a python script that will trace route an IP address and discover all the routers in the path to the target IP address.
6- We build the required knowledge about TCP protocol, how a connection is made during TCP handshake, and how to scan a target host to discover its open ports using TCP port scanning techniques. We write a python script to scan for open ports using TCP_SYN_SCAN, TCP_ACK_SCAN, TCP_FIN_SCAN...
7- We learn how to connect to a target machine and get a shell terminal to execute commands on this target machine, using BIND SHELL and REVERSE SHELL. We write a BIND SHELL and REVERSE SHELL using python scripting.
8- We learn the fundamentals skills about Cryptography, like Data Encoding, Data Hashing, Data Encryption/Decryption, and Password Hash Cracking.
9- We apply the theoretical knowledge about Cryptography by implementing an Hybrid Encryption in Python using RSA Asymmetric Encryption and AES Symmetric Encryption.
10- We write a Password Hash Cracking Tool using Python Scripting.
Who this course is for:
- Beginners and cyber security enthusiasts who want to follow an Ethical Hacking career
- System administrators and network administrators who aim to improve the defense of their infrastructure
User Reviews
Rating
Bilel Chatti
Instructor's Courses
Udemy
View courses Udemy- language english
- Training sessions 52
- duration 4:30:02
- Release Date 2023/09/10