Metasploit: Hands-on Guide to Pentesting with Metasploit
Packt Publishing
8:20:33
Description
Get started with the Metasploit Framework to access and test your system's security & create threat-free environment
What You'll Learn?
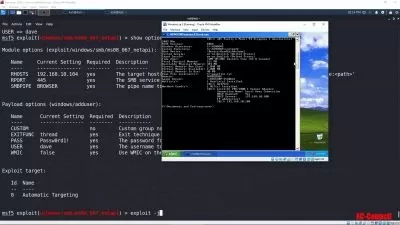
- Get to know the absolute basics of the Metasploit framework
- Set up the Metasploit environment along with your own virtual testing lab.
- Deep dive into Metasploit for information gathering and enumeration before planning the blueprint for the attack on the target system.
- Leverage Metasploit capabilities to perform Web application security scanning.
- Find and exploit vulnerabilities in networks and web applications effectively.
- Perform Vulnerability assessment and Penetration testing with Metasploit
- Attack on a remote machine using group of exploits.
Who is this for?
More details
DescriptionMetasploit is a popular penetration testing framework and has one of the largest exploit databases around. It is also called as playground for hackers where they demonstrate their skill by protecting or damaging the target. So if you wish to to carry out elementary penetration testing in highly secured environments then, this course is for you!
With this easy to digest practical guide to Metasploit, you will first learn how to correctly configure Metasploit & how to troubleshoot potential errors, as well as scan the different services to identify vulnerabilities. Then you will learn to find weaknesses in the target system and hunt for vulnerabilities using Metasploit and its supporting tools. Along with this, learn how hackers use the network to gain access to different systems. Moving on, you will gain deep knowledge about web application security scanning and bypassing anti-virus and clearing traces on the target system post-compromise. Finally, you'll explore how exploits and payloads work together to gain access to systems.
By end of this course you will be able to use Metasploit to quickly assess the security structure of systems and networks to reduce risk.
Contents and Overview
This training program includes 2 complete courses, carefully chosen to give you the most comprehensive training possible.
The first course, Beginning Metasploit teaches you the practical implementation of Metasploit. Each section will get you started with Metasploit by enumerating available services, identifying potential weaknesses, and testing vulnerabilities through exploitation. The course will show you how to correctly configure Metasploit and how to troubleshoot potential errors. You will scan the different services to identify vulnerabilities. Finally, you will explore sophisticated, real-world scenarios where performing penetration tests is a challenge.
The second course, Learning Metasploit will begin by introducing you to Metasploit and its functionality. Next, you will learn how to set up and configure Metasploit on various platforms to create a virtual test environment. You will also get your hands on various tools and components used by Metasploit. Further, in the video, you will learn how to find weaknesses in the target system and hunt for vulnerabilities using Metasploit and its supporting tools. Next, you'll get hands-on experience carrying out client-side attacks. Moving on, you'll learn about web application security scanning and bypassing anti-virus and clearing traces on the target system post-compromise. This video will also keep you updated with the latest security techniques and methods that can be directly applied to scan, test, hack, and secure networks and systems with Metasploit. By the end of this course, you'll get the hang of bypassing different defences, after which you'll learn how hackers use the network to gain access to different systems.
The third course, Hands-On Penetration Testing with Metasploit will help you explore several supporting tools on Kali Linux. Next, you'll explore how exploits and payloads work together to gain access to systems. Finally, you'll learn how Metasploit Framework works. By the end of this course, you'll have a better understanding of how to use Metasploit to quickly assess the security posture of systems and networks to reduce the risk of attack.
About the Authors:Â Â Â Â
Alexis Ahmed is an experienced Ethical Hacker and Cyber Security Expert with over 6 years' experience, He also develops Android apps and games in his free time. In addition, he is also a Web Developer with over 4 years' experience and he loves creating beautiful and functional websites for clients all over the world. He also has a YouTube channel with over 60,000 subscribers (and more than 2 million views!) where he makes videos on Ethical Hacking, Linux, and programming.
Sagar Rahalkar is a seasoned information security professional having more than 10 years of comprehensive experience in various verticals of IS. His domain expertise is mainly into breach detection, cybercrime investigations, digital forensics, application security, vulnerability assessment and penetration testing, compliance for mandates and regulations, IT GRC, and much more. He holds a master’s degree in computer science and several industry-recognized certifications such as Certified Cyber Crime Investigator, Certified Ethical Hacker, Certified Security Analyst, ISO 27001 Lead Auditor, IBM certified Specialist-Rational AppScan, Certified Information Security Manager (CISM), and PRINCE2. He has been closely associated with Indian law enforcement agencies for more than 3 years dealing with digital crime investigations and related training and received several awards and appreciation from senior officials of the police and defence organizations in India. Sagar has also been a reviewer and author for various books and online publications
Sunil Gupta;He is a Certified Ethical Hacker. Currently he teaches 50,000+ students online in 150+ countries. He is a specialist in the Ethical Hacking and Cyber Security areas. Author strengths – Vulnerability Assessment, Penetration Testing, Intrusion Detection, Risk Identification, Data Analysis, Report and Briefing.
Who this course is for:
- This course is aimed at penetration tester, ethical hacker, or security consultant who wants to understand the Metasploit framework and carry out penetration testing in highly secured environments.
Metasploit is a popular penetration testing framework and has one of the largest exploit databases around. It is also called as playground for hackers where they demonstrate their skill by protecting or damaging the target. So if you wish to to carry out elementary penetration testing in highly secured environments then, this course is for you!
With this easy to digest practical guide to Metasploit, you will first learn how to correctly configure Metasploit & how to troubleshoot potential errors, as well as scan the different services to identify vulnerabilities. Then you will learn to find weaknesses in the target system and hunt for vulnerabilities using Metasploit and its supporting tools. Along with this, learn how hackers use the network to gain access to different systems. Moving on, you will gain deep knowledge about web application security scanning and bypassing anti-virus and clearing traces on the target system post-compromise. Finally, you'll explore how exploits and payloads work together to gain access to systems.
By end of this course you will be able to use Metasploit to quickly assess the security structure of systems and networks to reduce risk.
Contents and Overview
This training program includes 2 complete courses, carefully chosen to give you the most comprehensive training possible.
The first course, Beginning Metasploit teaches you the practical implementation of Metasploit. Each section will get you started with Metasploit by enumerating available services, identifying potential weaknesses, and testing vulnerabilities through exploitation. The course will show you how to correctly configure Metasploit and how to troubleshoot potential errors. You will scan the different services to identify vulnerabilities. Finally, you will explore sophisticated, real-world scenarios where performing penetration tests is a challenge.
The second course, Learning Metasploit will begin by introducing you to Metasploit and its functionality. Next, you will learn how to set up and configure Metasploit on various platforms to create a virtual test environment. You will also get your hands on various tools and components used by Metasploit. Further, in the video, you will learn how to find weaknesses in the target system and hunt for vulnerabilities using Metasploit and its supporting tools. Next, you'll get hands-on experience carrying out client-side attacks. Moving on, you'll learn about web application security scanning and bypassing anti-virus and clearing traces on the target system post-compromise. This video will also keep you updated with the latest security techniques and methods that can be directly applied to scan, test, hack, and secure networks and systems with Metasploit. By the end of this course, you'll get the hang of bypassing different defences, after which you'll learn how hackers use the network to gain access to different systems.
The third course, Hands-On Penetration Testing with Metasploit will help you explore several supporting tools on Kali Linux. Next, you'll explore how exploits and payloads work together to gain access to systems. Finally, you'll learn how Metasploit Framework works. By the end of this course, you'll have a better understanding of how to use Metasploit to quickly assess the security posture of systems and networks to reduce the risk of attack.
About the Authors:Â Â Â Â
Alexis Ahmed is an experienced Ethical Hacker and Cyber Security Expert with over 6 years' experience, He also develops Android apps and games in his free time. In addition, he is also a Web Developer with over 4 years' experience and he loves creating beautiful and functional websites for clients all over the world. He also has a YouTube channel with over 60,000 subscribers (and more than 2 million views!) where he makes videos on Ethical Hacking, Linux, and programming.
Sagar Rahalkar is a seasoned information security professional having more than 10 years of comprehensive experience in various verticals of IS. His domain expertise is mainly into breach detection, cybercrime investigations, digital forensics, application security, vulnerability assessment and penetration testing, compliance for mandates and regulations, IT GRC, and much more. He holds a master’s degree in computer science and several industry-recognized certifications such as Certified Cyber Crime Investigator, Certified Ethical Hacker, Certified Security Analyst, ISO 27001 Lead Auditor, IBM certified Specialist-Rational AppScan, Certified Information Security Manager (CISM), and PRINCE2. He has been closely associated with Indian law enforcement agencies for more than 3 years dealing with digital crime investigations and related training and received several awards and appreciation from senior officials of the police and defence organizations in India. Sagar has also been a reviewer and author for various books and online publications
Sunil Gupta;He is a Certified Ethical Hacker. Currently he teaches 50,000+ students online in 150+ countries. He is a specialist in the Ethical Hacking and Cyber Security areas. Author strengths – Vulnerability Assessment, Penetration Testing, Intrusion Detection, Risk Identification, Data Analysis, Report and Briefing.
Who this course is for:
- This course is aimed at penetration tester, ethical hacker, or security consultant who wants to understand the Metasploit framework and carry out penetration testing in highly secured environments.
User Reviews
Rating
Packt Publishing
Instructor's Courses
Udemy
View courses Udemy- language english
- Training sessions 73
- duration 8:20:33
- English subtitles has
- Release Date 2023/02/20