Learn Wi-Fi Password Penetration Testing (WEP/WPA/WPA2)
Zaid Sabih,z Security
5:57:18
Description
46+ Videos to teach you how to hack and secure Wi-Fi (WEP, WPA, WPA2, WPA/WPA2 Enterprise)
What You'll Learn?
- Learn the main weaknesses of WEP encryption and how it can be cracked
- Understand a number of techniques to crack WEP,WPA & WPA2
- Gain access to WPA2 Enterprise networks.
- Hack captive portals (eg: hotel and airport networks).
- Use the GPU for faster cracking
- Have a good understanding of how networks operate
- Understand how devices communicate with each other in a netowrk
- Launch chopchop reply attack to crack WEP encryption
- Discover wireless networks within range
- Gather information about wifi networks
- Discover connected devices to each wifi network within range
- Disconnect any device from any network within range
- Launch interactive packet reply attack to crack WEP encryption
- Launch fragmentation attack to crack WEP encryption
- Learn WPA/WPA2 weakness and the theory behind cracking it
- Exploit WPS feature to crack WPA/WPA2 without a wordlist and without the need to any connected clients
- Capture handshake and launch word list attack
- Create your own wordlist
- Launch a wordlist attack using the GPU
- Launch a word list attack using a rainbow table
- How to protect wireless networks from cracking attacks
- Spot weaknesses in wireless networks in order to protect your network
- Configure wireless networks to protect against the discussed attacks
Who is this for?
What You Need to Know?
More details
DescriptionWelcome to my WiFi cracking course where you'll learn how to crack the key and get the password to WiFi networks weather they use WEP, WPA or even WPA2, not only that but you'll also learn how to secure networks from hackers.
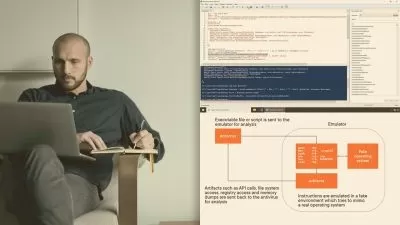
This course is highly practical but won't neglect the theory, you will start as a beginner with no prior knowledge about hacking, and it will take you through the basics of networking and how clients communicate with each other, how the different types of WiFi encryptions work, then you'll learn how to use this information to exploit these networks and crack their encryption.
The course is divided into four main sections:Â
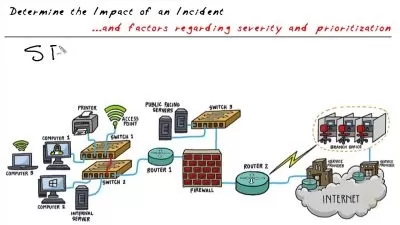
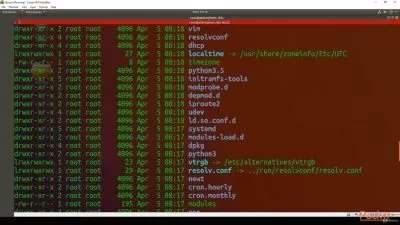
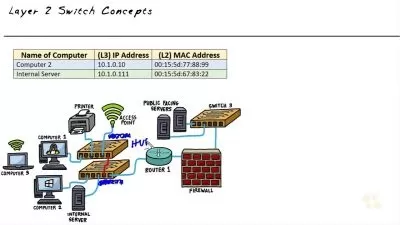
Networks Basics: in this section you will learn about how networks work, how devices communicate with each other and how the information is transferred in a wireless networks. You will also learn about basic terminology, what is a channel ? MAC address ? what is managed mode ? What is monitor mode and how to enable it ? what is sniffing and what is it limited to ? so in this section we still don't know much about penetration testing , all we have is a computer and a wireless card connected to it, you will learn how to start gathering information using your wi-fi card (packet sniffing) and you will learn a number of attacks that you can launch without the need to know the password such as controlling all the connections around you (ie: deny/allow any device from connecting to any network),  you will also learn how to overcome some security features that would prevent you from even trying any attacks, you will learn how to discover and target hidden networks and bypass mac filtering weather it is implemented using a black-list or a white-list. .
Â
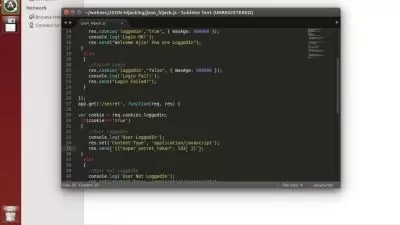
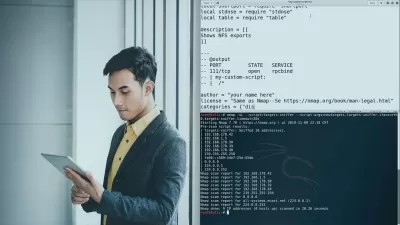
WEP Cracking: Now that you have gathered information about all the networks around you, and found your target, you will learn how to crack the key that the target uses. In this section you will learn four methods to crack WEP encryption. First you will learn the weaknesses in WEP that allow us to crack it, then you will learn the theory behind each method and finally you will learn how to launch that attack against WEP networks and obtain the key, in this section you will learn 4 different methods to crack WEP to make sure that you can crack any WEPÂ network you face regardless of how its configured.
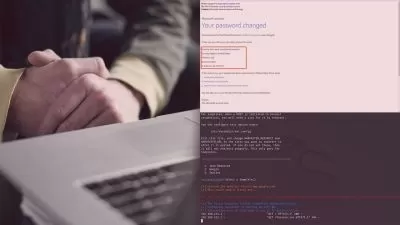
WPA Cracking: in this section you will learn a number of methods to crack WPA/WPA2 networks, again you will learn the weakness in WPA and theory behind each method first, and then you will learn how to launch the attack against a real network, this section is divided into a number of smaller sections:
Exploiting WPS - In this subsection you will learn how to exploit the WPS feature to gain access to WPA/WPA2 networks without using a wordlist, not only that but you'll also learn how to debug reaver's output and exploit the WPS feature on more routers using reaver's advanced options, you will also learn how to unlock some routers if they lock after a number of failed attempts.
Wordlist Attacks - in this subsection you will learn how to run wordlist attacks to crack the WPA/WPA2 key, you will learn how to use huge wordlists without wasting storage, save the cracking progress so that you can pause and resume the cracking process whenever you want, and you will also learn how to crack the key much faster using the GPU instead of the CPU.
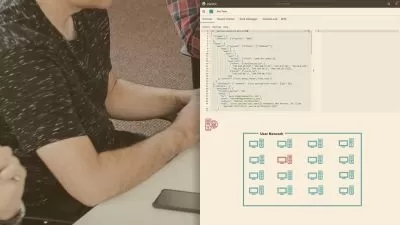
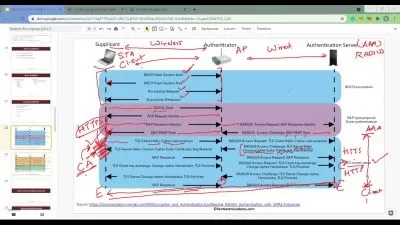
WPA/WPA2 Enterprise - These networks are usually used in companies and colleges, these are secure networks that use WPA/WPA2 but also require users to login with a username and password after connecting, in this subsection you will understand how they work and how to gain access to them.
Protection: At this stage you will know the weaknesses and methods that real life hackers use, therefore it will be very easy for you to secure your network against these attacks. In this section you will learn how to configure your wireless networks so that the above attacks will not work, you will learn what settings need to be changed, how to access the router settings and how to change these settings.
All the attacks in this course are practical attacks that work against real wireless networks in my lab
With this course you'll get 24/7 support, so if you have any questions you can post them in the Q&A section and we'll respond to you within 15 hours.
NOTE: This course is totally a product of Zaid Sabih and No other organization is associated for certification exam for the same. Although, you will receive Course Completion Certification from Udemy, apart from that No OTHER ORGANIZATION IS INVOLVED.Â
Who this course is for:
- People interested in learning how to test the security of WiFi keys/passwords
Welcome to my WiFi cracking course where you'll learn how to crack the key and get the password to WiFi networks weather they use WEP, WPA or even WPA2, not only that but you'll also learn how to secure networks from hackers.
This course is highly practical but won't neglect the theory, you will start as a beginner with no prior knowledge about hacking, and it will take you through the basics of networking and how clients communicate with each other, how the different types of WiFi encryptions work, then you'll learn how to use this information to exploit these networks and crack their encryption.
The course is divided into four main sections:Â
Networks Basics: in this section you will learn about how networks work, how devices communicate with each other and how the information is transferred in a wireless networks. You will also learn about basic terminology, what is a channel ? MAC address ? what is managed mode ? What is monitor mode and how to enable it ? what is sniffing and what is it limited to ? so in this section we still don't know much about penetration testing , all we have is a computer and a wireless card connected to it, you will learn how to start gathering information using your wi-fi card (packet sniffing) and you will learn a number of attacks that you can launch without the need to know the password such as controlling all the connections around you (ie: deny/allow any device from connecting to any network),  you will also learn how to overcome some security features that would prevent you from even trying any attacks, you will learn how to discover and target hidden networks and bypass mac filtering weather it is implemented using a black-list or a white-list. .
ÂWEP Cracking: Now that you have gathered information about all the networks around you, and found your target, you will learn how to crack the key that the target uses. In this section you will learn four methods to crack WEP encryption. First you will learn the weaknesses in WEP that allow us to crack it, then you will learn the theory behind each method and finally you will learn how to launch that attack against WEP networks and obtain the key, in this section you will learn 4 different methods to crack WEP to make sure that you can crack any WEPÂ network you face regardless of how its configured.
WPA Cracking: in this section you will learn a number of methods to crack WPA/WPA2 networks, again you will learn the weakness in WPA and theory behind each method first, and then you will learn how to launch the attack against a real network, this section is divided into a number of smaller sections:
Exploiting WPS - In this subsection you will learn how to exploit the WPS feature to gain access to WPA/WPA2 networks without using a wordlist, not only that but you'll also learn how to debug reaver's output and exploit the WPS feature on more routers using reaver's advanced options, you will also learn how to unlock some routers if they lock after a number of failed attempts.
Wordlist Attacks - in this subsection you will learn how to run wordlist attacks to crack the WPA/WPA2 key, you will learn how to use huge wordlists without wasting storage, save the cracking progress so that you can pause and resume the cracking process whenever you want, and you will also learn how to crack the key much faster using the GPU instead of the CPU.
WPA/WPA2 Enterprise - These networks are usually used in companies and colleges, these are secure networks that use WPA/WPA2 but also require users to login with a username and password after connecting, in this subsection you will understand how they work and how to gain access to them.
Protection: At this stage you will know the weaknesses and methods that real life hackers use, therefore it will be very easy for you to secure your network against these attacks. In this section you will learn how to configure your wireless networks so that the above attacks will not work, you will learn what settings need to be changed, how to access the router settings and how to change these settings.
All the attacks in this course are practical attacks that work against real wireless networks in my lab
With this course you'll get 24/7 support, so if you have any questions you can post them in the Q&A section and we'll respond to you within 15 hours.
NOTE: This course is totally a product of Zaid Sabih and No other organization is associated for certification exam for the same. Although, you will receive Course Completion Certification from Udemy, apart from that No OTHER ORGANIZATION IS INVOLVED.Â
Who this course is for:
- People interested in learning how to test the security of WiFi keys/passwords
User Reviews
Rating
Zaid Sabih
Instructor's Coursesz Security
Instructor's Courses
Udemy
View courses Udemy- language english
- Training sessions 48
- duration 5:57:18
- English subtitles has
- Release Date 2023/08/24