Learn Ethical Hacking From Scratch
Zaid Sabih,z Security
15:41:17
Description
Become an ethical hacker that can hack like black hat hackers and secure systems like cybersecurity experts
What You'll Learn?
- 145+ videos (15+ hours) to teach you ethical hacking & cybersecurity from scratch.
- Use 30+ hacking tools such as Metasploit, Aircrack-ng, SQLmap, etc.
- 85+ hands-on real-life hacking examples.
- No prior knowledge required
- Hack & secure WiFi & wired networks.
- Hack cloud servers.
- Create backdoors & Hack Windows.
- Start from 0 up to a high-intermediate level.
- Discover & exploit web application vulnerabilities to hack websites.
- Learn Network Hacking / Penetration Testing.
- Learn about the different hacking fields & hackers.
- Install a hacking lab & needed software (on Windows, OS X and Linux).
- Discover vulnerabilities & exploit them to hack into servers.
- Hack secure systems using client-side & social engineering.
- Secure systems from all the attacks shown.
- Install & use Kali Linux - a hacking operating system.
- Linux basics.
- Linux commands
- How to use the Linux terminal.
- Network basics & how devices interact inside a network.
- Run attacks on networks without knowing its key.
- Control Wi-Fi connections without knowing the password.
- Create a fake Wi-Fi network with internet connection & spy on clients.
- Gather detailed information about networks & connected clients like their OS, ports ...etc.
- Crack WEP/WPA/WPA2 encryptions.
- ARP Spoofing / ARP Poisoning.
- Launch various Man In The Middle attacks.
- Access any account accessed by any client on the network.
- Sniff network traffic & analyse it to extract important info such as: passwords, cookies, urls, videos, images ..etc.
- Intercept network traffic & modify it on the fly.
- Discover devices connected to the same network.
- Inject Javascript in pages loaded by clients connected to the same network.
- Redirect DNS requests to any destination (DNS spoofing).
- Secure networks from the discussed attacks.
- Edit router settings for maximum security.
- Discover suspicious activities in networks.
- How to prevent MITM attacks.
- Discover open ports, installed services and vulnerabilities on computer systems.
- Exploit buffer over flows & code execution vulnerabilities to gain control over systems.
- Hack systems using client side attacks.
- Hack Windows using fake updates.
- Backdoor normal programs.
- Backdoor any file type such as pictures, pdf's ...etc.
- Gather information about people, such as emails, social media accounts, emails and friends.
- Hack secure systems using social engineering.
- Send emails from ANY email account without knowing the password for that account.
- Analyse malware.
- Manually detect undetectable malware.
- Read, write download, upload and execute files on compromised systems.
- Capture keystrikes on a compromised system.
- Use a compromised computer as a pivot to hack other systems.
- Understand how websites & web applications work.
- Understand how browsers communicate with websites.
- Gather sensitive information about websites.
- Discover servers, technologies & services used on target website.
- Discover emails & sensitive data associated with a specific website.
- Discover subdomains associated with a website.
- Discover unpublished directories & files associated with a target website.
- Discover websites hosted on the same server as the target website.
- Exploit file upload vulnerabilities to gain control over target website.
- Discover, exploit and fix code execution vulnerabilities.
- Discover, exploit & fix local file inclusion vulnerabilities.
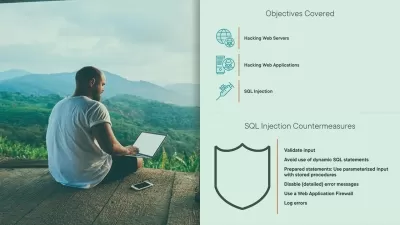
- Discover, exploit & fix SQL injection vulnerabilities.
- Bypass login forms and login as admin using SQL injections.
- Exploit SQL injections to find databases, tables & sensitive data such as usernames, passwords...etc
- Read / Write files to the server using SQL injections.
- Learn the right way to write SQL queries to prevent SQL injections.
- Discover reflected XSS vulnerabilities.
- Discover Stored XSS vulnerabilities.
- Hook victims to BeEF using XSS vulnerabilities.
- Fix XSS vulnerabilities & protect yourself from them as a user.
- Discover MITM & ARP Spoofing attacks.
Who is this for?
What You Need to Know?
More details
DescriptionWelcome this comprehensive Ethical Hacking course! This course assumes you have NO prior knowledge! It starts with you from scratch and takes you step-by-step teaching you how to hack systems like black-hat hackers and secure them like security experts!
This course is highly practical but it won't neglect the theory; we'll start with ethical hacking basics, breakdown the different penetration testing fields and install the needed software (on Windows, Linux and Apple Mac OS), then we'll dive and start hacking straight away. You'll learn everything by example, by analysing and exploiting different systems such as networks, cloud servers, clients, websites, etc. No boring dry lectures.
The course is divided into a number of sections, each section covers a penetration testing / hacking field, in each of these sections you'll first learn how the target system works, the weaknesses of this system, and how to practically exploit theses weaknesses to hack this system. As we do this I will also introduce you to different hacking and security concepts, tools and techniques. Everything will be taught through examples and hands-on practicals, there will be no useless or boring lectures!
All the techniques in this course are practical and work against real systems, you'll understand the whole mechanism of each technique first, then you'll learn how to use it to hack the target system . By the end of the course you'll be able to modify these techniques to launch more powerful attacks, and adopt them to suit different situations and different scenarios .
By the end of the course you will have a strong foundation in most hacking or penetration testing fields and you'll also learn how to detect, prevent and secure systems and yourself from the discussed attacks.Â
The course is divided into four main sections:Â Â
1. Network Hacking - This section will teach you how to hack and secure both wired & wireless networks. First, you will learn network basics, how they work, and how devices communicate with each other. Then it will branch into three sub sections: Â
Pre-connection attacks: in this subsection you'll learn a number of attacks that can be executed without connecting to the target network and without the need to know the network password; you'll learn how to gather information about the networks around you, discover connected devices, and control connections (deny/allow devices from connecting to networks).
Gaining Access: Now that you gathered information about the networks around you, in this subsection you will learn how to crack the key and get the password to your target network whether it uses WEP, WPA or even WPA2 .
Post Connection attacks: Now that you have the key, you can connect to the target network, in this subsection you will learn a number of powerful techniques that allow you to gather comprehensive information about the connected devices, see anything they do on the internet (such as login information, passwords, visited urls, images, videos, etc.), redirect requests, inject evil code in loaded pages and much more! You will also learn how to create a fake WiFi network or a honeypot, attract users to connect to it and use all of the above techniques against the connected clients.
2. Gaining Access - In this section you will learn two main approaches to gain remote access or hack computer systems:
Server Side Attacks:  In this subsection you will learn how to gain full access to computer systems without user interaction. You will learn how to gather useful information about a target system such as the operating system, open ports, installed services, then use this information to discover weaknesses / vulnerabilities and exploit them to gain full control over the target. Finally you will learn how to automatically scan servers for vulnerabilities and generate different types of reports with your discoveries.
Client Side Attacks - If the target system does not contain any weaknesses then the only way to hack it is by interacting with the users, in this subsection you'll learn how to get the target user to install a backdoor on their system without even realising, this is done by hijacking software updates or backdooring downloads on the fly. This subsection also teaches you how to use social engineering to hack secure systems, so you'll learn how to gather comprehensive information about system users such as their social accounts, friends, their mails, etc. You'll learn how to create trojans by backdooring normal files (such as an image or a pdf) and use the gathered information to spoof emails so they appear as if they're sent from the target's friend, boss or any email account they're likely to interact with, to social engineer them into running your trojan.
3. Post Exploitation - In this section you will learn how to interact with the systems you compromised so far. You’ll learn how to access the file system (read/write/upload/execute), maintain your access, spy on the target (capture key strikes, turn on the webcam, take screenshots, etc.) and even use the target computer as a pivot to hack other systems.
4. Website / Web Application Hacking - In this section you will learn how websites work, how to gather information about a target website (such as website owner, server location, used technologies, etc.) and how to discover and exploit the following dangerous vulnerabilities to hack websites:
Information Disclosure.
File Upload.
Code Execution.
Local File Inclusion.
Remote File Inclusion.
SQL Injection.
Cross Site Scripting (XSS).
Throughout the course you'll learn how to use use the following tools to achieve the above:
VMware.
Kali Linux
Nmap.
Bettercap.
Wireshark.
OWASP Zap.
Metasploit.
Nexpose.
SQLmap.
Maltego.
Veil Framework.
Crunch.
Netdiscover.
Zenmap.
arpspoof.
Evilgrade.
The Backdoor Factory.
BeEF.
Dirb.
Knockpy.
Netcat.
Aircrack-ng suite .
Airmon-ng .
Airodump-ng .
Aireplay-ng .
Aircrack-ng .
At the end of each section you will learn how to detect, prevent and secure systems and yourself from the discussed attacks.Â
Checkout the curriculum and the course teaser for more info!
With this course you'll get 24/7 support, so if you have any questions you can post them in the Q&A section and we'll respond to you within 15 hours.
 Â
Notes:
This course is created for educational purposes only, all the attacks are launched in my own lab or against systems that I have permission to test.
This course is totally a product of Zaid Sabih & zSecurity and no other organisation is associated with it or a certification exam. Although, you will receive a Course Completion Certification from Udemy, apart from that NO OTHER ORGANISATION IS INVOLVED.
Who this course is for:
- Anybody interested in learning ethical hacking / penetration testing
- Anybody interested in learning how hackers hack computer systems
- Anybody interested in learning how to secure systems from hackers
Welcome this comprehensive Ethical Hacking course! This course assumes you have NO prior knowledge! It starts with you from scratch and takes you step-by-step teaching you how to hack systems like black-hat hackers and secure them like security experts!
This course is highly practical but it won't neglect the theory; we'll start with ethical hacking basics, breakdown the different penetration testing fields and install the needed software (on Windows, Linux and Apple Mac OS), then we'll dive and start hacking straight away. You'll learn everything by example, by analysing and exploiting different systems such as networks, cloud servers, clients, websites, etc. No boring dry lectures.
The course is divided into a number of sections, each section covers a penetration testing / hacking field, in each of these sections you'll first learn how the target system works, the weaknesses of this system, and how to practically exploit theses weaknesses to hack this system. As we do this I will also introduce you to different hacking and security concepts, tools and techniques. Everything will be taught through examples and hands-on practicals, there will be no useless or boring lectures!
All the techniques in this course are practical and work against real systems, you'll understand the whole mechanism of each technique first, then you'll learn how to use it to hack the target system . By the end of the course you'll be able to modify these techniques to launch more powerful attacks, and adopt them to suit different situations and different scenarios .
By the end of the course you will have a strong foundation in most hacking or penetration testing fields and you'll also learn how to detect, prevent and secure systems and yourself from the discussed attacks.Â
The course is divided into four main sections:Â Â
1. Network Hacking - This section will teach you how to hack and secure both wired & wireless networks. First, you will learn network basics, how they work, and how devices communicate with each other. Then it will branch into three sub sections: Â
Pre-connection attacks: in this subsection you'll learn a number of attacks that can be executed without connecting to the target network and without the need to know the network password; you'll learn how to gather information about the networks around you, discover connected devices, and control connections (deny/allow devices from connecting to networks).
Gaining Access: Now that you gathered information about the networks around you, in this subsection you will learn how to crack the key and get the password to your target network whether it uses WEP, WPA or even WPA2 .
Post Connection attacks: Now that you have the key, you can connect to the target network, in this subsection you will learn a number of powerful techniques that allow you to gather comprehensive information about the connected devices, see anything they do on the internet (such as login information, passwords, visited urls, images, videos, etc.), redirect requests, inject evil code in loaded pages and much more! You will also learn how to create a fake WiFi network or a honeypot, attract users to connect to it and use all of the above techniques against the connected clients.
2. Gaining Access - In this section you will learn two main approaches to gain remote access or hack computer systems:
Server Side Attacks:  In this subsection you will learn how to gain full access to computer systems without user interaction. You will learn how to gather useful information about a target system such as the operating system, open ports, installed services, then use this information to discover weaknesses / vulnerabilities and exploit them to gain full control over the target. Finally you will learn how to automatically scan servers for vulnerabilities and generate different types of reports with your discoveries.
Client Side Attacks - If the target system does not contain any weaknesses then the only way to hack it is by interacting with the users, in this subsection you'll learn how to get the target user to install a backdoor on their system without even realising, this is done by hijacking software updates or backdooring downloads on the fly. This subsection also teaches you how to use social engineering to hack secure systems, so you'll learn how to gather comprehensive information about system users such as their social accounts, friends, their mails, etc. You'll learn how to create trojans by backdooring normal files (such as an image or a pdf) and use the gathered information to spoof emails so they appear as if they're sent from the target's friend, boss or any email account they're likely to interact with, to social engineer them into running your trojan.
3. Post Exploitation - In this section you will learn how to interact with the systems you compromised so far. You’ll learn how to access the file system (read/write/upload/execute), maintain your access, spy on the target (capture key strikes, turn on the webcam, take screenshots, etc.) and even use the target computer as a pivot to hack other systems.
4. Website / Web Application Hacking - In this section you will learn how websites work, how to gather information about a target website (such as website owner, server location, used technologies, etc.) and how to discover and exploit the following dangerous vulnerabilities to hack websites:
Information Disclosure.
File Upload.
Code Execution.
Local File Inclusion.
Remote File Inclusion.
SQL Injection.
Cross Site Scripting (XSS).
Throughout the course you'll learn how to use use the following tools to achieve the above:
VMware.
Kali Linux
Nmap.
Bettercap.
Wireshark.
OWASP Zap.
Metasploit.
Nexpose.
SQLmap.
Maltego.
Veil Framework.
Crunch.
Netdiscover.
Zenmap.
arpspoof.
Evilgrade.
The Backdoor Factory.
BeEF.
Dirb.
Knockpy.
Netcat.
Aircrack-ng suite .
Airmon-ng .
Airodump-ng .
Aireplay-ng .
Aircrack-ng .
At the end of each section you will learn how to detect, prevent and secure systems and yourself from the discussed attacks.Â
Checkout the curriculum and the course teaser for more info!
With this course you'll get 24/7 support, so if you have any questions you can post them in the Q&A section and we'll respond to you within 15 hours.
 Â
Notes:
This course is created for educational purposes only, all the attacks are launched in my own lab or against systems that I have permission to test.
This course is totally a product of Zaid Sabih & zSecurity and no other organisation is associated with it or a certification exam. Although, you will receive a Course Completion Certification from Udemy, apart from that NO OTHER ORGANISATION IS INVOLVED.
Who this course is for:
- Anybody interested in learning ethical hacking / penetration testing
- Anybody interested in learning how hackers hack computer systems
- Anybody interested in learning how to secure systems from hackers
User Reviews
Rating
Zaid Sabih
Instructor's Coursesz Security
Instructor's Courses
Udemy
View courses Udemy- language english
- Training sessions 143
- duration 15:41:17
- Release Date 2024/04/13