KALI For Ethical Hacking: Learn KALI From Scratch
IT Security Online Training
6:57:37
Description
Learn Kali for Anonymity, hacking, cracking, Nmap, Security and much more....
What You'll Learn?
- Learn Kali From Scratch
- Learn WiFi hacking using Kali
- Learn Hash and Password Cracking
- Learn Windows Hacking and More
Who is this for?
More details
DescriptionKALI v2022
- Why Kali?
Kali Linux is mainly used for Penetration Testing and Security Auditing. Kali contains several hundred tools which are geared towards various information security tasks, such as Penetration Testing, Security research, Computer Forensics and Reverse Engineering.
- Anonymity?
Learn user friendly tools to maximise Anonymity. Protect your identity while surfing online.
- Vulnerability Analysis?
Vulnerability assessmentâ€â€also called vulnerability analysisâ€â€is a process that identifies, quantifies and analyse security weaknesses in IT infrastructure. We will find and exploit systems using weakness.
- Database Assessment?
We will use free tools inbuilt in Kali to perform database assessment.
- Wireless Attacks?
We will perform Brute Force attack on Wi-Fi. We will also perform dictionary attack on wireless router. You will learn 7 Steps to hack any Wi-Fi based on WPA/WPA2.
- Other Exploitation?
Metasploit= It is an open source tool for performing an exploit against remote target machine.
Buffer Overflow= Perform buffer overflow attack using Metasploit.
Meterpreter= Meterpreter is a security product used for penetration testing. Part of the Metasploit Project and Framework, it provides enterprise security teams with the knowledge helpful for addressing vulnerabilities in the targeted application against which Meterpreter is deployed.
Honeypot= A honeypot is a computer security mechanism set to detect, deflect, or, in some manner, counteract attempts at unauthorized use of information systems.
Who this course is for:
- Anyone who want to learn Kali
KALI v2022
- Why Kali?
Kali Linux is mainly used for Penetration Testing and Security Auditing. Kali contains several hundred tools which are geared towards various information security tasks, such as Penetration Testing, Security research, Computer Forensics and Reverse Engineering.
- Anonymity?
Learn user friendly tools to maximise Anonymity. Protect your identity while surfing online.
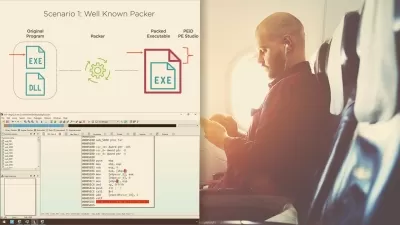
- Vulnerability Analysis?
Vulnerability assessmentâ€â€also called vulnerability analysisâ€â€is a process that identifies, quantifies and analyse security weaknesses in IT infrastructure. We will find and exploit systems using weakness.
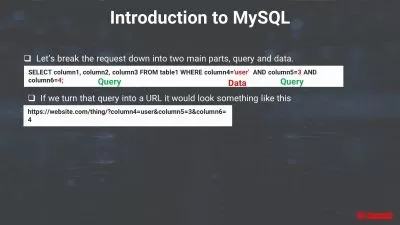
- Database Assessment?
We will use free tools inbuilt in Kali to perform database assessment.
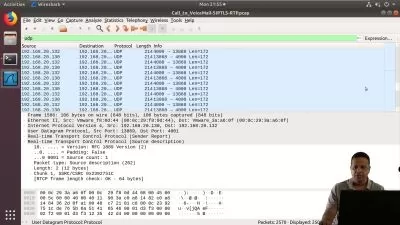
- Wireless Attacks?
We will perform Brute Force attack on Wi-Fi. We will also perform dictionary attack on wireless router. You will learn 7 Steps to hack any Wi-Fi based on WPA/WPA2.
- Other Exploitation?
Metasploit= It is an open source tool for performing an exploit against remote target machine.
Buffer Overflow= Perform buffer overflow attack using Metasploit.
Meterpreter= Meterpreter is a security product used for penetration testing. Part of the Metasploit Project and Framework, it provides enterprise security teams with the knowledge helpful for addressing vulnerabilities in the targeted application against which Meterpreter is deployed.
Honeypot= A honeypot is a computer security mechanism set to detect, deflect, or, in some manner, counteract attempts at unauthorized use of information systems.
Who this course is for:
- Anyone who want to learn Kali
User Reviews
Rating
IT Security Online Training
Instructor's Courses
Udemy
View courses Udemy- language english
- Training sessions 81
- duration 6:57:37
- Release Date 2023/04/10