Introduction to Cybersecurity with Practical Examples
2:17:46
Description
Cybersecurity Concepts and Principles, Cyber Threats and Attacks, Cryptographic, Compliance, Incident Response Technique
What You'll Learn?
- 1. Comprehend Core Cybersecurity Concepts and Principles
- 2. Identify and Understand Common Cyber Threats and Attacks
- 3. Apply Basic Network and Application Security Practices
- 4. Implement Essential Cryptographic, Compliance, and Incident Response Techniques
Who is this for?
What You Need to Know?
More details
DescriptionThis cybersecurity course, Introduction to Cybersecurity with Practical Examples, provides a comprehensive foundation in cybersecurity principles, methodologies, and real-world applications. It covers the core topics essential for anyone interested in protecting digital assets, whether at a personal, corporate, or governmental level.
The course begins with an introduction to cybersecurity, emphasizing the critical need for securing data, networks, and systems in an era of rising cybercrime. Learners are introduced to the fundamental principles of information security: confidentiality, integrity, and availability, with practical examples to illustrate each concept. Following this, the course explores various types of cyberattacks, such as malware, phishing, and DDoS, each with explicit, relatable scenarios to help students recognize these threats in real life.
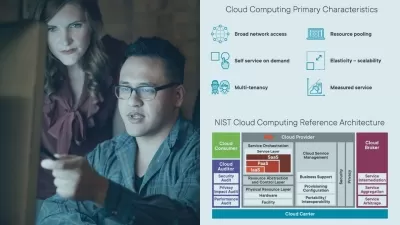
Next, networking basics are discussed, covering essential concepts like the OSI model, TCP/IP protocols, and network security elements like firewalls, VPNs, and IDS/IPS. The module also examines network attack methods such as spoofing and ARP poisoning, highlighting the need for robust network security practices.
Cryptography is another focus area, where learners explore symmetric and asymmetric encryption, hashing, and the role of Public Key Infrastructure (PKI). These are essential for protecting data integrity and securing communications. In Application Security, students gain insights into secure coding practices, session management, and common vulnerabilities, particularly those highlighted in the OWASP Top 10, such as SQL Injection and Cross-Site Scripting.
Further modules delve into Operating System Security and IoT Security, where students learn about access controls, patch management, and the unique security challenges of IoT devices. The course also covers Security Testing and Risk Assessment, emphasizing the importance of penetration testing, vulnerability scanning, and risk management.
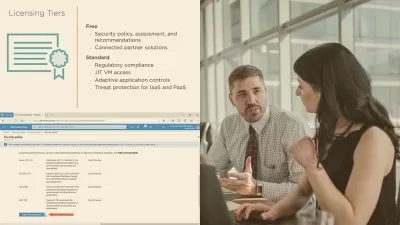
The course later discusses compliance regulations, like GDPR and HIPAA, incident response, and forensic investigation practices in later modules. Finally, current trends, such as AI in cybersecurity, the Zero Trust model, and the threat posed by ransomware and quantum computing, are explored. This comprehensive course will equip learners with the knowledge and skills to tackle cybersecurity challenges effectively.
Who this course is for:
- Beginners, students, pupils, and all people interested in Cybersecurity
This cybersecurity course, Introduction to Cybersecurity with Practical Examples, provides a comprehensive foundation in cybersecurity principles, methodologies, and real-world applications. It covers the core topics essential for anyone interested in protecting digital assets, whether at a personal, corporate, or governmental level.
The course begins with an introduction to cybersecurity, emphasizing the critical need for securing data, networks, and systems in an era of rising cybercrime. Learners are introduced to the fundamental principles of information security: confidentiality, integrity, and availability, with practical examples to illustrate each concept. Following this, the course explores various types of cyberattacks, such as malware, phishing, and DDoS, each with explicit, relatable scenarios to help students recognize these threats in real life.
Next, networking basics are discussed, covering essential concepts like the OSI model, TCP/IP protocols, and network security elements like firewalls, VPNs, and IDS/IPS. The module also examines network attack methods such as spoofing and ARP poisoning, highlighting the need for robust network security practices.
Cryptography is another focus area, where learners explore symmetric and asymmetric encryption, hashing, and the role of Public Key Infrastructure (PKI). These are essential for protecting data integrity and securing communications. In Application Security, students gain insights into secure coding practices, session management, and common vulnerabilities, particularly those highlighted in the OWASP Top 10, such as SQL Injection and Cross-Site Scripting.
Further modules delve into Operating System Security and IoT Security, where students learn about access controls, patch management, and the unique security challenges of IoT devices. The course also covers Security Testing and Risk Assessment, emphasizing the importance of penetration testing, vulnerability scanning, and risk management.
The course later discusses compliance regulations, like GDPR and HIPAA, incident response, and forensic investigation practices in later modules. Finally, current trends, such as AI in cybersecurity, the Zero Trust model, and the threat posed by ransomware and quantum computing, are explored. This comprehensive course will equip learners with the knowledge and skills to tackle cybersecurity challenges effectively.
Who this course is for:
- Beginners, students, pupils, and all people interested in Cybersecurity
User Reviews
Rating

Udemy
View courses Udemy- language english
- Training sessions 10
- duration 2:17:46
- Release Date 2025/03/11