Identity Management, Authentication, and Access Control with Squid
Zachary Bennett
21:35
Description
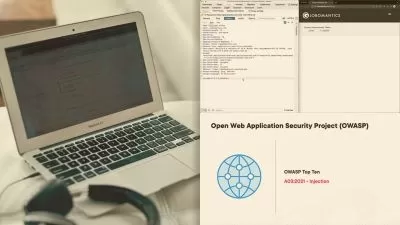
Squid is a widely used caching proxy that contains a robust set of authentication and access controls. In this course, you'll learn the setup, configuration, and validation of Squid in an enterprise environment.
What You'll Learn?
With the attack surface size of any given enterprise network, it is of the utmost importance that you take every step necessary when it comes to securing your web servers and proxies. One of the ways that you can protect your network is by managing user access and authentication properly. In this course, Identity Management, Authentication, and Access Control with Squid, you’ll cover how to utilize Squid to secure a live enterprise environment. First, you’ll demonstrate the ability to set up Squid as an HTTP proxy cache. Next, you’ll apply Squid configuration including access control list elements. Finally, you’ll simulate how to use access control lists and authentication mechanisms in order to use Squid securely. When you’re finished with this course, you’ll have the skills and knowledge needed to identify, protect, detect, or respond to threats in your network systems.
More details
User Reviews
Rating
Zachary Bennett
Instructor's Courses
Pluralsight
View courses Pluralsight- language english
- Training sessions 7
- duration 21:35
- level average
- English subtitles has
- Release Date 2023/07/25