Ethical Hacking + Website Hacking + Mobile Hacking: CYBERPRO
Shubham Pareek
5:49:28
Description
Learn the Art of System Hacking, Website Hacking, Mobile Hacking and Forensics with Linux Course, Ethical Hacking Course
What You'll Learn?
- You will learn all the important aspects of Ethical Hacking
- You will also learn about Website Penetration Testing
- You will learn about Bug Bounty
- Mobile Hacking Forensics Practicals
- Practical Approach and Live Training
- Live Website Hacking
- Both Defensive and Offensive attacks explained
Who is this for?
What You Need to Know?
More details
DescriptionEthical Hacking + Website Hacking + Mobile Hacking and Forensics + Linux for Beginners: 4 in 1 Cyber Security Course
1. Ethical Hacking:
Footprinting >Â Scanning > Gaining Access > Maintaining Access >Â Clearing Tracks > Generating Reports
Footprinting: It is a technique used for gathering information about computer systems and the entities they belong to. To get this information, a hacker might use various tools and technologies. This information is very useful to a hacker who is trying to crack a whole system.
Scanning: It can be considered a logical extension of active reconnaissance since the attacker uses details gathered during reconnaissance to identify specific vulnerabilities. Attackers can gather critical network information such as the mapping of systems, routers, and firewalls with simple tools like Traceroute. Port scanners can be used to detect listening ports to find information about the nature of services running on the target machine.
Gaining Access: In this phase, hacker designs the blueprint of the network of the target with the help of data collected during Phase 1 and Phase 2. The hacker has finished enumerating and scanning the network and now decide that they have some options to gain access to the network.
Maintaining Access: Once a hacker has gained access, they want to keep that access for future exploitation and attacks. Once the hacker owns the system, they can use it as a base to launch additional attacks. The longer a Hacker is able to maintain access the more information He may able to gather.
Clearing Tracks:Â No thief wants to get caught, Prior to the attack, the attacker would change their MAC address and run the attacking machine through at least one VPN to help cover their identity, So no one can reach them.
Generating Reports:Â Reports are a summary of your work deliver to management. You have to include what tools or techniques you have used during pen-testing and what results you got. You have t include screenshots if possible and classify threats on the basis of severity.
2. Website Hacking:
Basics to Advanced Attacks= SQL + XSS + DoS & DDoS
3. Mobile Hacking:
Learn the art of recovering deleted data and also learn about mobile forensics
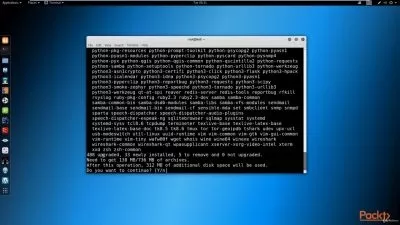
4. Linux for Beginners:
Additional Content Provided to help you learn Linux Operating System
After Completing all of the above courses you will become a Cyber Security Professional.
Learn how Black Hat attacks and How you can Defend, as well as fight back.
5. Additional Content:
Learn to create a website in 30 seconds using AI
Let's get started.
Who this course is for:
- People want to become a Cyber Security Expert
- Students who want to become Ethical Hacker
- People want to learn Bug Hunting
- Anyone who want to learn Internet Security
Ethical Hacking + Website Hacking + Mobile Hacking and Forensics + Linux for Beginners: 4 in 1 Cyber Security Course
1. Ethical Hacking:
Footprinting >Â Scanning > Gaining Access > Maintaining Access >Â Clearing Tracks > Generating Reports
Footprinting: It is a technique used for gathering information about computer systems and the entities they belong to. To get this information, a hacker might use various tools and technologies. This information is very useful to a hacker who is trying to crack a whole system.
Scanning: It can be considered a logical extension of active reconnaissance since the attacker uses details gathered during reconnaissance to identify specific vulnerabilities. Attackers can gather critical network information such as the mapping of systems, routers, and firewalls with simple tools like Traceroute. Port scanners can be used to detect listening ports to find information about the nature of services running on the target machine.
Gaining Access: In this phase, hacker designs the blueprint of the network of the target with the help of data collected during Phase 1 and Phase 2. The hacker has finished enumerating and scanning the network and now decide that they have some options to gain access to the network.
Maintaining Access: Once a hacker has gained access, they want to keep that access for future exploitation and attacks. Once the hacker owns the system, they can use it as a base to launch additional attacks. The longer a Hacker is able to maintain access the more information He may able to gather.
Clearing Tracks:Â No thief wants to get caught, Prior to the attack, the attacker would change their MAC address and run the attacking machine through at least one VPN to help cover their identity, So no one can reach them.
Generating Reports:Â Reports are a summary of your work deliver to management. You have to include what tools or techniques you have used during pen-testing and what results you got. You have t include screenshots if possible and classify threats on the basis of severity.
2. Website Hacking:
Basics to Advanced Attacks= SQL + XSS + DoS & DDoS
3. Mobile Hacking:
Learn the art of recovering deleted data and also learn about mobile forensics
4. Linux for Beginners:
Additional Content Provided to help you learn Linux Operating System
After Completing all of the above courses you will become a Cyber Security Professional.
Learn how Black Hat attacks and How you can Defend, as well as fight back.
5. Additional Content:
Learn to create a website in 30 seconds using AI
Let's get started.
Who this course is for:
- People want to become a Cyber Security Expert
- Students who want to become Ethical Hacker
- People want to learn Bug Hunting
- Anyone who want to learn Internet Security
User Reviews
Rating
Shubham Pareek
Instructor's Courses
Udemy
View courses Udemy- language english
- Training sessions 69
- duration 5:49:28
- English subtitles has
- Release Date 2024/12/06