Ethical Hacking: Weaponization
Peter A
44:38
Description
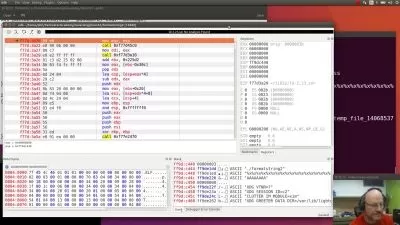
Hack using Office Douments
What You'll Learn?
- Hack PC using Word Document
- How to do VBA scripting
- Types of Reverse Shells
- How to use Meterpreter shell
Who is this for?
More details
DescriptionA hacker can simply break into a system to show that it is vulnerable, or he can be so mischievous that he wants to hold or maintain a connection in the background without the user's knowledge. This can happen with Trojan horses, rootkits, or other malicious files. The goal is to maintain access to the target until he completes the tasks he intends to perform in that target.
Cyber ​​attacks are not to be taken lightly. It doesn't matter if you have the most secure firewall in the world; every step in the cyber kill chain reduces your security and leads to breaches of your network. That's why it's so important to know how to spot an attack when it happens -- or ideally, stop it in the first place.
In this course you will learn how you can hack a computer using an office document and also using an html application. You'll learn how to create a reverse shell giving you complete access over the computer. You will be able to launch a reverse shell as soon as the user opens the office document. You will learn about metasploit too, a tool that is often used in computer hacking. You will learn how to use the metasploit console and use it to create a reverse shell.
This is a beginners course, you don't need any prior knowledge but some computer knowledge like Linux basics and networking is recommended.
Who this course is for:
- Beginner Ethical Hackers
A hacker can simply break into a system to show that it is vulnerable, or he can be so mischievous that he wants to hold or maintain a connection in the background without the user's knowledge. This can happen with Trojan horses, rootkits, or other malicious files. The goal is to maintain access to the target until he completes the tasks he intends to perform in that target.
Cyber ​​attacks are not to be taken lightly. It doesn't matter if you have the most secure firewall in the world; every step in the cyber kill chain reduces your security and leads to breaches of your network. That's why it's so important to know how to spot an attack when it happens -- or ideally, stop it in the first place.
In this course you will learn how you can hack a computer using an office document and also using an html application. You'll learn how to create a reverse shell giving you complete access over the computer. You will be able to launch a reverse shell as soon as the user opens the office document. You will learn about metasploit too, a tool that is often used in computer hacking. You will learn how to use the metasploit console and use it to create a reverse shell.
This is a beginners course, you don't need any prior knowledge but some computer knowledge like Linux basics and networking is recommended.
Who this course is for:
- Beginner Ethical Hackers
User Reviews
Rating
Peter A
Instructor's Courses
Udemy
View courses Udemy- language english
- Training sessions 8
- duration 44:38
- Release Date 2023/02/26