Creating a Shodan Clone for hackers and bug bounty hunters
Ismail cenk
7:04:34
Description
Build Your Own Shodan-Style Network Search Engine, great for hackers, bug bounty hunters, red/ blue team members.
What You'll Learn?
- How to find IPs behind WAF.
- How to scan millions of IP addresses super fast.
- Find new subdomains
- Make money by finding vulnerabilities.
- Increase your attack surface
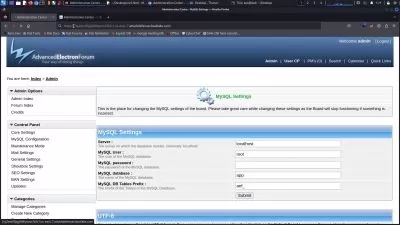
- Find vulnerable endpoints
- Find specific frameworks to attack
- Improve coding in Python programming language.
Who is this for?
What You Need to Know?
More details
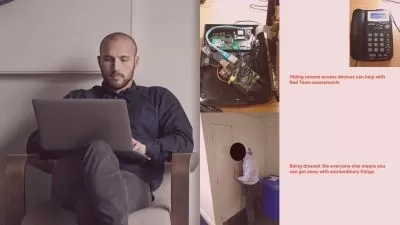
DescriptionUnlock the advanced techniques of network scanning and broaden your penetration testing capabilities with this comprehensive course. Designed for aspiring ethical hackers and security enthusiasts, this course delves deep into the art of efficiently scanning millions of IP addresses and expanding the potential attack surface.
The scanner we will create is much more effective than Shodan/ Censys or any similar search engine, because it can also find many IPs, subdomains, frameworks of small companies. I ain't playing games here, this is not an average YouTube course or a simple course or a useless hacking certification course. This is a whole hacking massacre.
Basic Python knowledge is required. Please make sure that you have basic/beginner python knowledge as it may get very hard to understand the course. DO NOT copy and paste the code, if you don't watch ALL the course videos and just use the app I create you will fail. Understand the entire course, you can then do amazing things.
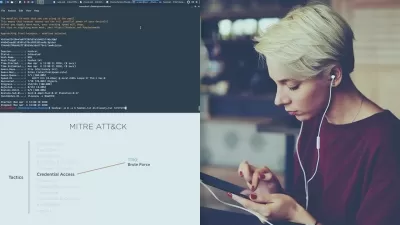
Mastering Network Scanning Techniques: Learn the ins and outs of various network scanning methodologies, including port scanning, host discovery, to gain a comprehensive view of your target network.
Efficient IP Address Enumeration: Acquire the skills to efficiently enumerate large sets of IP addresses, identifying potential entry points for penetration testing and vulnerability assessment.
Service Identification and Versioning: Hone your skills in identifying running services and their versions, enabling you to pinpoint specific vulnerabilities and potential avenues for exploitation.
Who Should Enroll:
Cybersecurity Enthusiasts
Ethical Hackers and Penetration Testers
Bug Bounty Hunters
IT Professionals Seeking Advanced Security Skills
Network Administrators Interested in Security
Students Pursuing a Career in Cybersecurity
Red team / Blue team members
Embark on a transformative journey to elevate your network scanning proficiency. By enrolling in this course, you'll gain exclusive access to advanced techniques that will revolutionize your approach to security assessments. Discover the nuanced art of efficient IP address enumeration and master the strategic expansion of the attack surface. These skills are pivotal for conducting highly effective penetration tests and in-depth vulnerability assessments.
Prepare to take your network scanning skills to the next level. Enroll now and unlock the secrets to efficient IP address enumeration for effective penetration testing and vulnerability assessment.
Who this course is for:
- Hackers
- Penetration testers
- Bug bounty hunters
- Red team members
- Blue team members
- Students who want to get into Cybersecurity
- Network engineers
Unlock the advanced techniques of network scanning and broaden your penetration testing capabilities with this comprehensive course. Designed for aspiring ethical hackers and security enthusiasts, this course delves deep into the art of efficiently scanning millions of IP addresses and expanding the potential attack surface.
The scanner we will create is much more effective than Shodan/ Censys or any similar search engine, because it can also find many IPs, subdomains, frameworks of small companies. I ain't playing games here, this is not an average YouTube course or a simple course or a useless hacking certification course. This is a whole hacking massacre.
Basic Python knowledge is required. Please make sure that you have basic/beginner python knowledge as it may get very hard to understand the course. DO NOT copy and paste the code, if you don't watch ALL the course videos and just use the app I create you will fail. Understand the entire course, you can then do amazing things.
Mastering Network Scanning Techniques: Learn the ins and outs of various network scanning methodologies, including port scanning, host discovery, to gain a comprehensive view of your target network.
Efficient IP Address Enumeration: Acquire the skills to efficiently enumerate large sets of IP addresses, identifying potential entry points for penetration testing and vulnerability assessment.
Service Identification and Versioning: Hone your skills in identifying running services and their versions, enabling you to pinpoint specific vulnerabilities and potential avenues for exploitation.
Who Should Enroll:
Cybersecurity Enthusiasts
Ethical Hackers and Penetration Testers
Bug Bounty Hunters
IT Professionals Seeking Advanced Security Skills
Network Administrators Interested in Security
Students Pursuing a Career in Cybersecurity
Red team / Blue team members
Embark on a transformative journey to elevate your network scanning proficiency. By enrolling in this course, you'll gain exclusive access to advanced techniques that will revolutionize your approach to security assessments. Discover the nuanced art of efficient IP address enumeration and master the strategic expansion of the attack surface. These skills are pivotal for conducting highly effective penetration tests and in-depth vulnerability assessments.
Prepare to take your network scanning skills to the next level. Enroll now and unlock the secrets to efficient IP address enumeration for effective penetration testing and vulnerability assessment.
Who this course is for:
- Hackers
- Penetration testers
- Bug bounty hunters
- Red team members
- Blue team members
- Students who want to get into Cybersecurity
- Network engineers
User Reviews
Rating
Ismail cenk
Instructor's Courses
Udemy
View courses Udemy- language english
- Training sessions 15
- duration 7:04:34
- Release Date 2023/12/16