Access Control, Cloud Security and Penetration Testing
ExamIT -Sonia
4:08:48
Description
Access Control, Cloud Security and Penetration Testing for Cybersecurity professionals
What You'll Learn?
- Learn about access control mechanisms, such as access control lists (ACLs), authentication, authorization, and accountability.
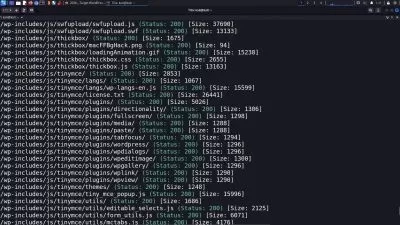
- Understand the objectives, methodologies, and tools used in penetration testing to assess the security posture of systems and networks.
- Learn about penetration testing phases, including reconnaissance, scanning, exploitation, and post-exploitation.
- Develop practical skills in conducting penetration tests, identifying vulnerabilities, and recommending remediation measures.
Who is this for?
What You Need to Know?
More details
DescriptionThis course provides a comprehensive exploration of access control mechanisms, cloud security principles, and penetration testing methodologies in the field of cybersecurity. Participants will delve into the concepts, techniques, and best practices associated with controlling access to information systems, securing cloud environments, and conducting penetration tests to identify and remediate security vulnerabilities. Through a combination of theoretical lectures, hands-on labs, and real-world simulations, learners will develop the knowledge and skills necessary to design, implement, and assess access control measures, cloud security configurations, and penetration testing strategies.
Course Objectives:
Understand the principles of access control and its importance in safeguarding information systems and resources.
Explore access control models, including discretionary access control (DAC), mandatory access control (MAC), and role-based access control (RBAC).
Learn about access control mechanisms, such as access control lists (ACLs), authentication, authorization, and accountability.
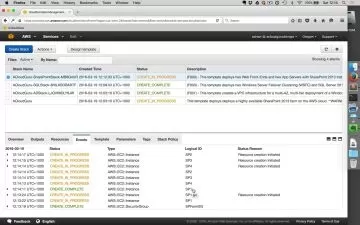
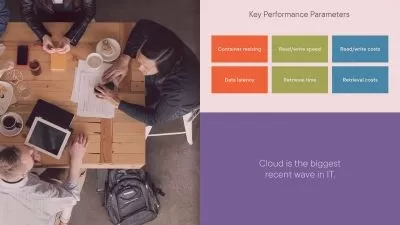
Gain insights into cloud computing fundamentals, cloud service models, and cloud deployment models.
Discover best practices for securing cloud environments, including identity and access management (IAM), encryption, and network security.
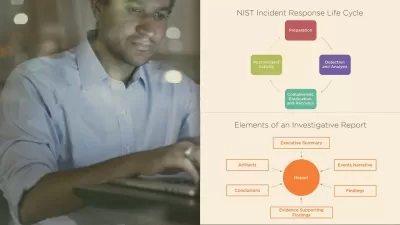
Understand the objectives, methodologies, and tools used in penetration testing to assess the security posture of systems and networks.
Learn about penetration testing phases, including reconnaissance, scanning, exploitation, and post-exploitation.
Develop practical skills in conducting penetration tests, identifying vulnerabilities, and recommending remediation measures.
Upon completion of this course, participants will be equipped with the knowledge and skills to effectively implement access control measures, secure cloud environments, and conduct penetration tests to assess and enhance the security posture of information systems and networks.
Who this course is for:
- Cybersecurity professionals seeking to enhance their knowledge and skills in access control, cloud security, and penetration testing.
- IT professionals responsible for implementing and managing access control systems, cloud environments, and security testing procedures.
This course provides a comprehensive exploration of access control mechanisms, cloud security principles, and penetration testing methodologies in the field of cybersecurity. Participants will delve into the concepts, techniques, and best practices associated with controlling access to information systems, securing cloud environments, and conducting penetration tests to identify and remediate security vulnerabilities. Through a combination of theoretical lectures, hands-on labs, and real-world simulations, learners will develop the knowledge and skills necessary to design, implement, and assess access control measures, cloud security configurations, and penetration testing strategies.
Course Objectives:
Understand the principles of access control and its importance in safeguarding information systems and resources.
Explore access control models, including discretionary access control (DAC), mandatory access control (MAC), and role-based access control (RBAC).
Learn about access control mechanisms, such as access control lists (ACLs), authentication, authorization, and accountability.
Gain insights into cloud computing fundamentals, cloud service models, and cloud deployment models.
Discover best practices for securing cloud environments, including identity and access management (IAM), encryption, and network security.
Understand the objectives, methodologies, and tools used in penetration testing to assess the security posture of systems and networks.
Learn about penetration testing phases, including reconnaissance, scanning, exploitation, and post-exploitation.
Develop practical skills in conducting penetration tests, identifying vulnerabilities, and recommending remediation measures.
Upon completion of this course, participants will be equipped with the knowledge and skills to effectively implement access control measures, secure cloud environments, and conduct penetration tests to assess and enhance the security posture of information systems and networks.
Who this course is for:
- Cybersecurity professionals seeking to enhance their knowledge and skills in access control, cloud security, and penetration testing.
- IT professionals responsible for implementing and managing access control systems, cloud environments, and security testing procedures.
User Reviews
Rating
ExamIT -Sonia
Instructor's Courses
Udemy
View courses Udemy- language english
- Training sessions 9
- duration 4:08:48
- Release Date 2024/06/21